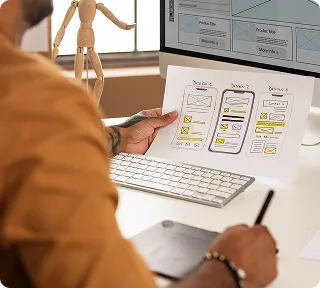
We assess iOS and Android applications for security vulnerabilities including insecure data storage, weak encryption, and API exploitation. Our mobile vapt service includes reverse engineering, code analysis, runtime testing, and communication security validation.
Mobile apps store sensitive user data, handle payments, and access corporate systems making them attractive targets for attackers. We test mobile security comprehensively. Our assessment covers local data storage, network communication encryption, certificate pinning, jailbreak detection, code obfuscation, and API authentication ensuring your mobile app protects user data even on compromised devices.



















































 AI-Powered Vulnerability Prioritization
AI-Powered Vulnerability Prioritization Automated Threat Modeling
Automated Threat Modeling Smart Exploit Generation
Smart Exploit Generation Predictive Security Analytics
Predictive Security Analytics